Update your hypervisor before get bitten by venom

Security Researchers at CrowdStrike Discovered vulnerability in virtual floppy drive used by many virtualization platform like KVM and QEMU . flaw is presented since first ever code implemented for virtual floppy drive .
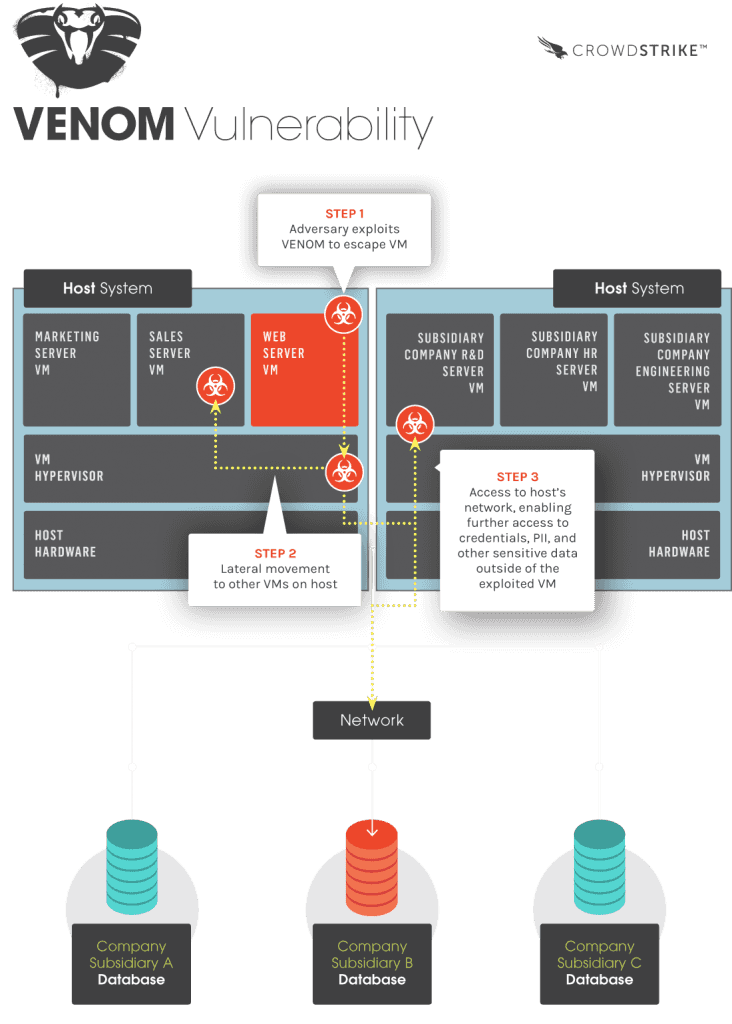
This vulnerability may allow an attacker to escape from the confines of an affected virtual machine (VM) guest and potentially obtain code-execution access to the host .
vulnerability details
The guest operating system communicates with the FDC by sending commands such as seek, read, write, format, etc. to the FDC’s input/output port. QEMU’s virtual FDC uses a fixed-size buffer for storing these commands and their associated data parameters. The FDC keeps track of how much data to expect for each command and, after all expected data for a given command is received from the guest system, the FDC executes the command and clears the buffer for the next command.
This buffer reset is performed immediately at the completion of processing for all FDC commands, except for two of the defined commands. An attacker can send these commands and specially crafted parameter data from the guest system to the FDC to overflow the data buffer and execute arbitrary code in the context of the host’s hypervisor process.
— Source
How to fix
According to venom vulnerability information website , vendors released patches for affected products , just update and upgrade your system .
for Debian based systems
sudo apt-get update
sudo apt-get upgradefor redhat and fedora
yum update
yum update qemu-kvmaffected Products
- QEMU
- KVM
- Xen Hypervisors
Not Affected Products
- VMware
- Microsoft Hyper-V
- Bochs hypervisors
- Xen ARM systems are not vulnerable
More Information http://venom.crowdstrike.com/
Redhat Knowledge Base : https://access.redhat.com/articles/1444903
Redhat Bugzilla : https://bugzilla.redhat.com/show_bug.cgi?id=1218611