Test and fix glibc GHOST vulnerability in Linux Server
Recently critical security vulnerability has been discovered in glibc library , CVE ID: CVE-2015-0235 , according redhat security advisory ” gethostbyname function can be exploited by using crafted hostname which will lead to buffer overflow .
this vulnerability in glibc library allow attackers to execute remote arbitrary codes in any affected system , gethostbyname function can be exploited by using crafted hostname which will lead to buffer overflow .
first vulnerable version of the GNU C Library is glibc-2.2
Test Your Server
snippet from : http://www.openwall.com/lists/oss-security/2015/01/27/9
#include <netdb.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <errno.h>
#define CANARY "in_the_coal_mine"
struct {
char buffer[1024];
char canary[sizeof(CANARY)];
} temp = { "buffer", CANARY };
int main(void) {
struct hostent resbuf;
struct hostent *result;
int herrno;
int retval;
/*** strlen (name) = size_needed - sizeof (*host_addr) - sizeof (*h_addr_ptrs) - 1; ***/
size_t len = sizeof(temp.buffer) - 16*sizeof(unsigned char) - 2*sizeof(char *) - 1;
char name[sizeof(temp.buffer)];
memset(name, '0', len);
name[len] = '';
retval = gethostbyname_r(name, &resbuf, temp.buffer, sizeof(temp.buffer), &result, &herrno);
if (strcmp(temp.canary, CANARY) != 0) {
puts("vulnerable");
exit(EXIT_SUCCESS);
}
if (retval == ERANGE) {
puts("not vulnerable");
exit(EXIT_SUCCESS);
}
puts("should not happen");
exit(EXIT_FAILURE);
}Compile This and run
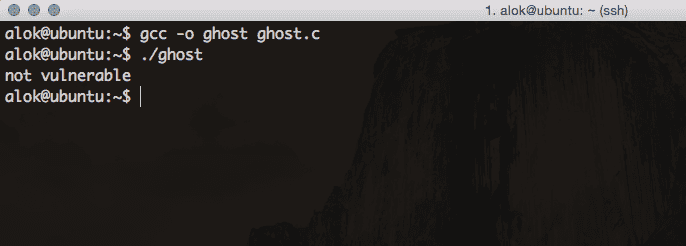
$ gcc -o ghost ghost.c Sample Output
List of affected Linux Distros ( credits : http://www.cyberciti.biz/faq/cve-2015-0235-patch-ghost-on-debian-ubuntu-fedora-centos-rhel-linux/ )
- RHEL (Red Hat Enterprise Linux) version 5.x, 6.x and 7.x
- CentOS Linux version 5.x, 6.x & 7.x
- Ubuntu Linux version 10.04, 12.04 LTS
- Debian Linux version 7.x
- Linux Mint version 13.0
- Fedora Linux version 19 or older
- SUSE Linux Enterprise 11 and older (also OpenSuse Linux 11 or older versions).
- Arch Linux glibc version < = 2.18-1
Fix
mostly all vendors are rolling out fixed version of glibc , just update and upgrade your distro
for debian based users
sudo apt-get update
sudo apt-get upgradeThen REBOOT ( to make sure all running instances take effect )
sudo rebootfor redhat
sudo yum update
sudo rebootafter that verify installed version of glibc
dpkg -s libc6sample output
Package: libc6
Status: install ok installed
Priority: required
Section: libs
Installed-Size: 10497
Maintainer: Ubuntu Developers <[email protected]>
Architecture: amd64
Multi-Arch: same
Source: eglibc
Version: 2.19-0ubuntu6.3
Replaces: libc6-amd64
Provides: glibc-2.19-1
Depends: libgcc1
Suggests: glibc-doc, debconf | debconf-2.0, locales
Breaks: hurd (<< 1:0.5.git20140203-1), lsb-core (<= 3.2-27), nscd (<< 2.19)
Conflicts: prelink (<= 0.0.20090311-1), tzdata (<< 2007k-1), tzdata-etch
Conffiles:
/etc/ld.so.conf.d/x86_64-linux-gnu.conf 593ad12389ab2b6f952e7ede67b8fbbf
Description: Embedded GNU C Library: Shared libraries
Contains the standard libraries that are used by nearly all programs on
the system. This package includes shared versions of the standard C library
and the standard math library, as well as many others.
Homepage: http://www.eglibc.org
Original-Maintainer: GNU Libc Maintainers <[email protected]>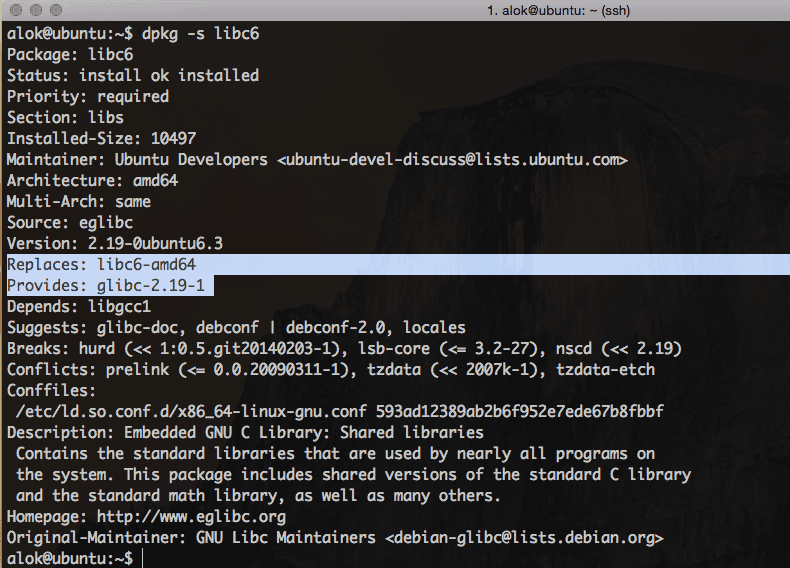
Redhat Advisory : https://access.redhat.com/solutions/1334663
Detailed vulnerability Info : http://www.openwall.com/lists/oss-security/2015/01/27/9